🎉 New update! Get our latest insights.
Strengthen Your Network with Proactive Defense
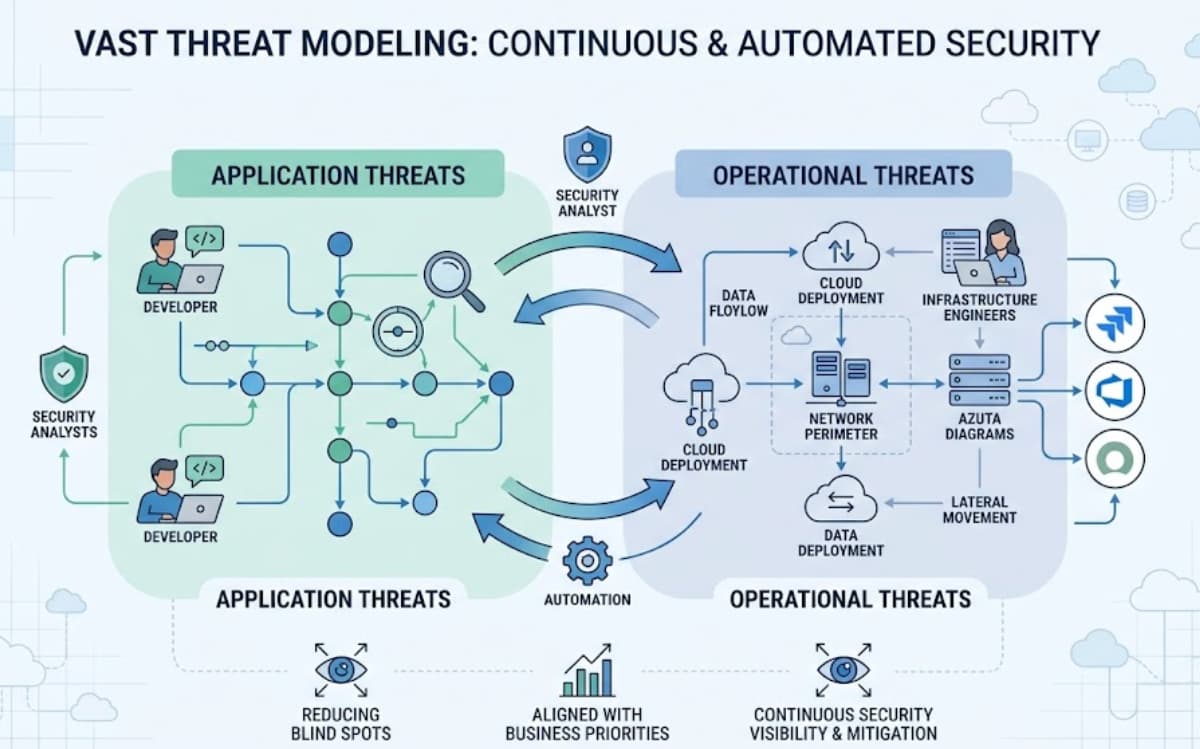
Onboard threat modeling and risk analysis into your security workflow stay ahead of attackers with deep insights tailored to your organization’s unique threat landscape.




From 1200+ Clients

Trusted by Cybersecurity Teams, Enterprises & Government Agencies
Helping SOC teams, threat analysts, and CISOs detect blind spots before attackers do.

Make Confident Security Decisions
Focus on the threats that actually matter. Prioritize risk based on impact, likelihood, and compliance alignment.

Model Threats & Reduce Risk Exposure Faster
Streamline your security process with prebuilt models, automated scoring, and visual attack path simulations.

Stay Updated on Emerging Threats
Access continuously updated intelligence, CVE context, and mapped controls so you never fall behind.
Case Studies
See how leading organizations across industries use networkthreatdetection.com to strengthen their network defense, streamline risk management, and respond faster to evolving threats.
How a Healthcare Network Reduced Vulnerability by 57%
Using networkthreatdetection.com, the CISO team streamlined their vulnerability management process across 15+ hospital branches.
Financial Institution Cut Response Time by 72%
The platform helped the incident response team quickly identify lateral movement paths and contain threats within hours.
Best Features
Trusted Company

Ready to Build Proactive Network Defense?
- Schedule a demo with a threat modeling specialist.
Built for Threat-Focused Teams
NetworkThreatDetection.com provides a rich library of attack scenarios, mapped controls, and intuitive tools to close security gaps fast.
Threat modeling aligned with MITRE ATT&CK, STRIDE, and PASTA
Risk scoring based on asset criticality and exploit likelihood
Threat intelligence feeds to map CVEs to your environment
Executive and technical reports
Weekly OverWatch™ updates with real-world attack simulations

Emerging Threats & Technologies
Threat Model Library: See It in Action
Explore real examples of how our threat models help visualize risks and map attack paths across different environments.
Attack Surface Mapping in ICS & OT Environments
Identify vulnerabilities across industrial systems and operational tech environments.
Hybrid Cloud Environment Threat Model
Understand risks in mixed cloud/on-prem setups with multi-vector threat mapping.
Internal Network Lateral Movement Map
Track how attackers can pivot across internal assets and escalate privileges.
In-Depth Threat Model for Healthcare Network Protection
Model threats targeting sensitive medical data and critical infrastructure.
Enterprise Office Network Threat Model
Spot vulnerabilities in corporate LAN/WAN setups, email systems, and endpoints.
Zero Trust Architecture Threat Model
Test your zero-trust assumptions by simulating attacker behavior in micro-segmented networks.
What Our Users Say?

Security Engineer
The automated risk analysis and CVE mapping saved us hundreds of hours across audits and response workflows.

Security Analyst
It’s like having a threat intelligence analyst built into our SOC. The integration with our existing stack was seamless.

Incident Response Lead
This platform gives us confidence in our network architecture and lets us show real risk reduction to leadership.

CISO
The weekly threat model updates are a game changer. They help us stay aligned with evolving threats without overwhelming the team.

Cyber Risk Officer
We were blind to lateral movement paths until we used this platform. It gave us actionable insights that our traditional tools missed.

Network Security Manager
Latest Research & Insights
Ready to Elevate Your Network Security Strategy?
- Schedule a demo with our threat detection team.







The modeling clarity and attack path simulations are incredibly effective. We now know where we’re vulnerable—before attackers do.